Science & Nature
What is WannaCry? What You Need to Know About Latest Cyberattack
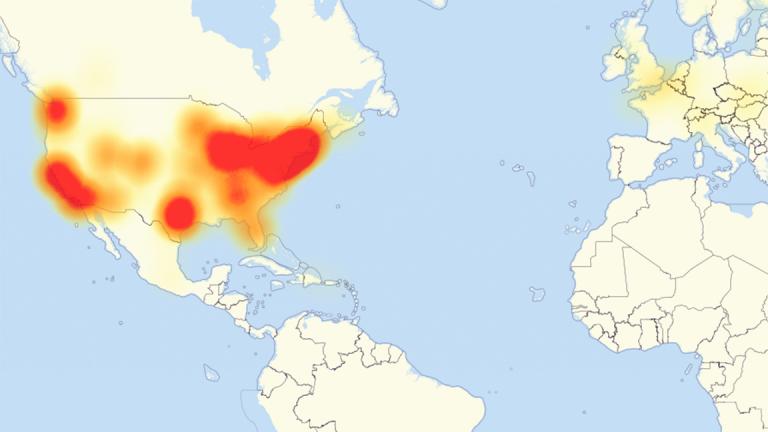
It may make you WannaCry if your business or home computer was hit in the latest cyberattack. This new ransomware attack began in Europe and has affected 200,000 computers in 150 countries. And even though there is a fix for it now, the widespread infiltration has inspired malware copy cats.
Joining host Carol Marin on Monday to discuss what exactly WannaCry is and how to protect your data is Jacob Furst, a professor at DePaul University’s College of Computing and Digital Media who is an expert in computer security and the director of the DePaul Information Assurance Center; Hardik Bhatt, Illinois' Chief Information Officer who is in charge of the state's new cybersecurity plan to guard against attacks on state agencies; and Sanjiv Bawa, CEO and founder of the Chicago-based technology infrastructure management, security and cloud hosting company, Chi Networks.
Below, a Q&A with Furst.
![]()
What is WannaCry?
It is a variety of malware called ransomware. It takes over your files. Your computer works fine, but if you try to look at files and folders on your machine, they are essentially not there.
Wait. The files are there but you can’t access them?
Yes. But they’ve been encrypted so they are literally random bits and bytes that’s basically garbage.
So ransomware scrambles it, but does not take it?
Right. It’s not typical that data is taken. It’s encrypted for subsequent payment.
How can you reverse the damage? Or can you make it work again?
You probably don’t get to reverse the damage. Bad guys say “send money” and then they’ll send you an encryption key but there’s disincentive for them to actually do that because they can then be tracked.
Is there a way to recover your data?
If you had done a backup on a disconnected hard drive at the time of the attack, you can recover the data. Otherwise, you’re files are toast.
Who is the WannaCry attack affecting?
This particular attack has hit a lot of people across the world. It’s largely hit businesses because they hadn’t patched software. Microsoft makes it easier for individuals to patch their computers. It’s harder for a lot of different businesses. It depends on their security posture. Many businesses keep backups and off site backups. But it’s possible to imagine the worst possible scenario.
What should people and businesses do?
The first order for people who are infected is that they need to get rid of malware with somebody who knows what they’re doing. You might have to reinstall the operating system. You then need to patch the operating system. Then reinstall the backups. Then you can move on to normal business and accept that you may lose a few days of data.
Any other recommendations?
In general, you should have an external hard drive that you back up and unplug from your machine. I had a hard drive that kept crashing, so I back up important files to an external hard drive. This extends to businesses, too. It’s actually standard procedure for any company that’s generally knowledgeable of security. Keep your operating system updated which is easier for individuals. For some businesses that’s tougher because they have hundreds or thousands of machines. Its standard operating procedure for businesses but it can take some time.
Will it cross platforms from Microsoft to Apple?
Not this one.
Who is behind the cyberattack?
No one has claimed credit for this. I’ve read that it may be small operator. The ransom was only $300, so probably not a state operator. It’s also probably not organized crime because the code is so poorly written. And if it is a small operator, I bet they are terrified by their success because now the whole world is after them.
Is cloud-based storage like Dropbox, Google Drive safer?
Yes. In general, cloud providers have an understanding of information security.
Is the attack over and done?
Yes and no. What typically happens with malware with this huge a splash, you’ll find copy cats. Most copy cats are not sophisticated. There’s always more coming.
![]()
Additional resources:
Ransomware victims urged to report infections to federal law enforcement
No more ransom project prevention advice
Related stories:
 Illinois’ Chief Information Officer on Cybersecurity
Illinois’ Chief Information Officer on Cybersecurity
March 29: How Hardik Bhatt wants to protect state agencies from hackers.
 How Everyday Home Devices Were Used to Shut Down Major Websites
How Everyday Home Devices Were Used to Shut Down Major Websites
Oct. 31, 2016: A massive cyberattack temporarily takes down major websites. Find out how hackers use household devices to wreak havoc online.
 Dialing Up Defenses to Cybersecurity
Dialing Up Defenses to Cybersecurity
Sept. 15, 2016: Whether fictional or real, stories of hacking appear to be everywhere. We discuss online security and the public’s fascination with hackers with two local experts.